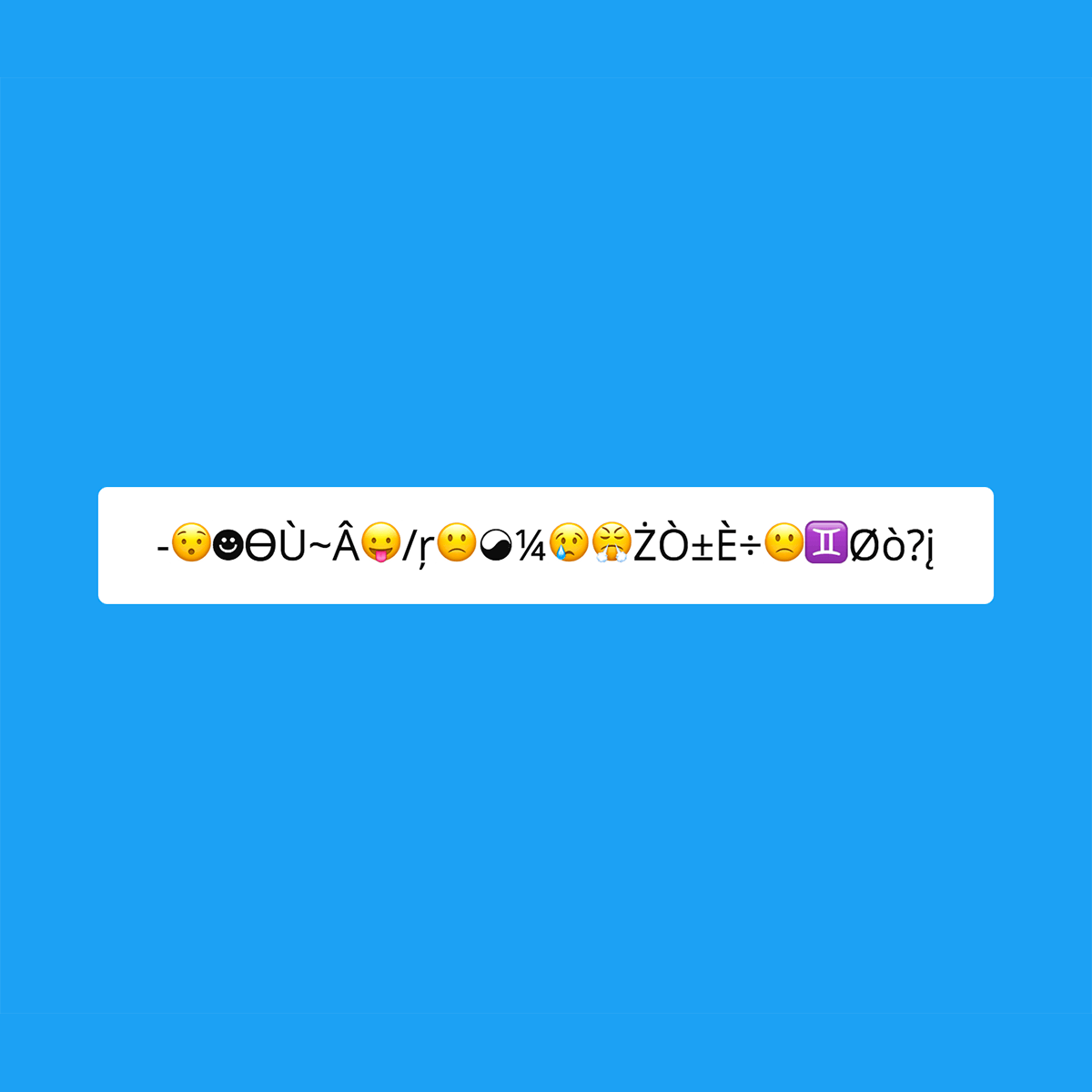
Strong & Secure Random Password Generator
...
Quickstart: Click "regen" multiple times, then click "copy" to copy the password to your clipboard. If you understand pseudo-random number generators feel free to modify the parameters below to your heart's content.

This strong random password generator creates strong random plain text passwords using the PCG32 random number generator without sending the password over the internet or storing the generated password on a server. If you are still uncomfortable using this utility you can generate multiple passwords, save them to your device and use different parts from each to create a unique password, otherwise you may want to try something like using the Python REPL to generate a strong password.
I developed this password generator because I don't trust the security and randomness of passwords generated by other password generators; plus, I like a challenge. I also wanted to test out Melissa E. O'Neill's implementation of the PCG32 pseudo-random number generator with an environment-based seed. By generating multiple passwords using this strong password generator, saving them to my local computer then mixing them I can confidently trust in the uniqueness and security of my passwords. The number of password breaches each year is staggering. By using a unique, random password for every account I can rest assured that even if one system is hacked all of my other accounts' passwords are safe.
I've also made a genuine effort to keep this page as simple as possible in order to reduce the attack surface. Feel free to inspect the page source and you'll find there are no javascript tracking scripts, no pixels, no cookies, no third-party resources, no ads, and no embedded social media. All variables are generated in-browser and not on the server-side and no requests are made when you click "generate", "copy" or when you modify the algroithm's parameters.
Pro Tips for Users
- Always use unique passwords for every account you have.
- Always use unique security questions and answers for every account you have.
- Never use the same password multiple times.
- Always ensure passwords are at a minimum sixteen characters long. The longer the better.
- Always ensure every password contains a mixture of uppercase letters, lowercase letters, numbers, punctuation and special symbols.
- Never use dictionary words, birthdays, family members' names, pets' names or any other easily guessable words in your passwords.
- Never use your address, postal code, phone number, ID card number, or other personally identifiable information in your passwords.
- Never use an easily guessed or commonly used password such as P@ssw0rd, $ecr3t or AbC!23.
- Never use similar passwords with mostly the same characters and only a few characters changed, because one comprimised password will still comprimize all of the other passwords. For example MyPassword4Gmail and MyPassword4Mac.
- Never share your password over text message, instant messenger, facebook, instagram, slack, discord or unencrypted email.
- Please don't write your password down on a sticky note and put it on your computer screen visible to others.
- If you're setting a password that must be memorized try using the first few letters of each word in a phrase.
- Never log in to an important account via public WiFi or on an untrusted device (e.g. friend's computer or mobile phone).
- Always make sure the site you are logging in to is encrypted with a secure certificate.
- Always make sure the site you are logging in to is the site you are expecting. Use bookmarks whenever possible.
- Do not trust entering your password into forms you arrived at by clicking a link in an email or private message.
- Change your passwords every two or three months, or in the event of a security breach, change your password immediately.
- Use two-factor-authentication or multi-factor-authentication whenever possible.
- Trust noone. Banks, website helpdesk personnel, your IT guy...noone. Never give out your password, ever.
- Do not store your more critical passwords unencrypted in the cloud. The cloud is not as safe as you think.
- Use a VPN whenever possible. If you are traveling, it is fairly easy to install and configure a single-user OpenVPN server that allows you to be in control of your connection's security.
- Do not trust your web browser to store your passwords in a secure manner.
- Always keep your computer, web browser, internet router, and devices up-to-date. Hackers can very easily exploit older versions.
- Use AntiVirus software. Just do it.
- Encrypt all drives connected to your computer
- Be careful when using online paste tools and screen capture tools, do not let them to upload your passwords to the cloud.
- Do not log in to critical accounts using another person's computer or using a shared computer.
- Lock your computer and mobile phone when you leave them.
Pro Tips for Developers
- Never generate users' passwords and transmit the generated passwords via email.
- Never store users' passwords, security questions and answers as plain text. Ever. I will find you if you do this, and I will say very unkind things to you.
- Always salt and hash passwords with unique, non-deterministic salt per user.
- Always log invalid login attempts and alert users of suspicious activity.
- Always lock accounts after several incorrect login attempts.
- Always use TLS with a valid, up-to-date certificate. Personally, I like certbot.
- Remember: the internet is a scary place filled with viruses, bugs, hackers, bots and the darkweb; let's not make it worse by building crappy password management systems.
- To prevent brute force login attacks on your dedicated, virtual private, or cloud servers install intrusion detection and prevention software. Both Palo Alto Networks and Alert Logic provide quite comprehensive solutions.
- Sign package updates with a private key using GnuPG and verify the signature of it with the public key published previously.
- Use your own domain for all user-facing interactions.
- Require VPN access for administrators.
- Restrict access using a firewall to any internal non-public facing servers and services.
- Finally, if any of this is confusing, ask questions. Go find a more senior developer and ask them how they would do it.
Also check out the Random Passphrase Generator, Unicode Random Password Generator, and How to Generate a Strong Random Password in Python.
-Sethers